This feature is in development. This documentation is published ahead of release to support feedback and discussion — the UI, CLI flags, and YAML schema described here are illustrative and subject to change. If you have questions or comments, please reach out to the Kosli team.
- Define a control library in Kosli that mirrors your existing controls catalog
- Record decision outcomes against controls from your pipelines
- Reference controls in environment policies
- View control compliance across deployments
Prerequisites
- Install Kosli CLI.
- Get a Kosli API token.
- Have at least one Flow and Trail already created.
Setup
Understanding controls
Before creating controls, it helps to understand how they fit into the Kosli data model. Raw fact attestations are the evidence you collect in pipelines — test results, vulnerability scans, pull request approvals. These are facts about what happened. Decisions are the recorded outcomes of a Policy Decision Point (PDP) — the step in your process where a judgement is reached about a specific control: “controlRCTL-043 is satisfied for this artifact.” A decision is an attestation that references a control, recorded at the point where the judgement is made — typically during a release or promotion step.
Controls are the named governance requirements that decisions are recorded against. They have a stable identity (the control identifier), a human-readable name, and an optional description and source link pointing back to your GRC system or policy document.
This separation matters: raw facts exist independently of controls. A JUnit test report is a fact. Whether that test report satisfies a “test coverage” control is a decision. The decision references the fact; the fact doesn’t need to know about the control.
A Policy Enforcement Point (PEP) is where that decision is acted upon. kosli assert artifact --environment is the PEP — it checks that an artifact satisfies all requirements in the environment’s policy, including any listed controls, and exits non-zero if it doesn’t. Place it at the point in your pipeline where you want to gate progress on control compliance.
Kosli holds a mirror to your existing control definitions — it does not replace your GRC system or ServiceNow instance. The control catalog in Kosli is a lightweight copy that enables querying and coverage visibility.
Creating a control
Navigate to Controls in the Kosli app sidebar and select New control. Provide a control identifier, a name, and optionally a description and a source URL pointing back to the authoritative definition in your GRC system or policy document. You can also create controls via the CLI:| Flag | Description |
|---|---|
--identifier | Required. The control identifier (e.g. RCTL-043, peer-review, vuln-scan-production). Must be unique within your organisation. Immutable once created — to change a control identifier, archive the control and create a new one. |
--name | Required. A human-readable label for the control (e.g. Source code review). Mutable — you can rename a control while keeping the same identifier. |
--description | Optional. What the control does, in human-readable terms. |
--source-url | Optional. URL back to the authoritative definition in your GRC system, ServiceNow, or policy document. |
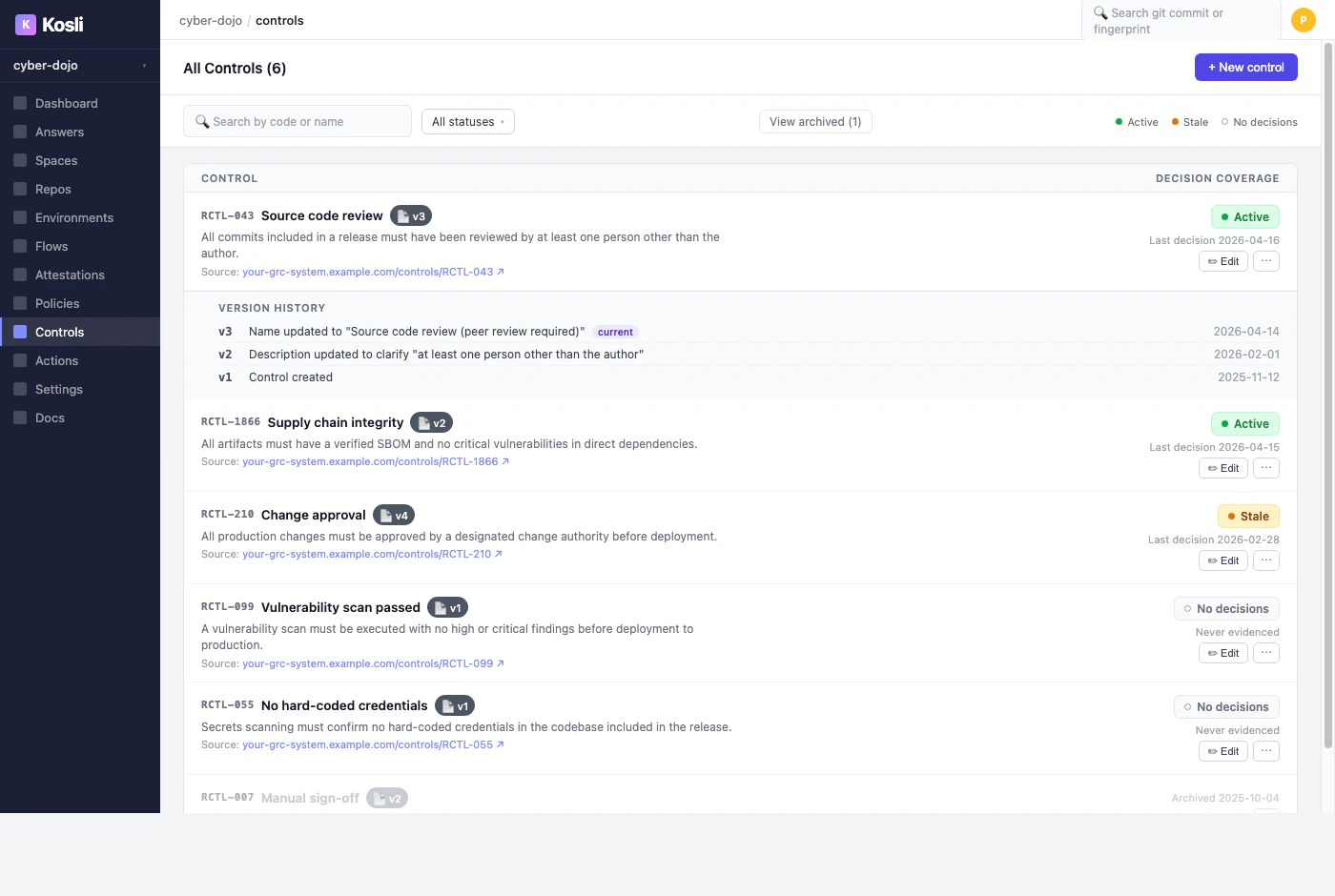
List your controls
Navigate to Controls in the Kosli app sidebar to browse your full controls catalog. Each control shows its code, name, current version, and a decision coverage indicator that reflects the health of that control across your pipelines. Control definitions are versioned: each time you update a control’s name, description, or source URL, a new version is created. This matters for audits — decisions recorded against a control always reference the exact version of the definition that was current when the decision was made, so the audit trail is precise even as controls evolve over time.| Status | Meaning |
|---|---|
| Active | A passing decision has been recorded against this control within the last 28 days. |
| Stale | Decisions were recorded in the past but none in the last 28 days — pipelines may have stopped recording decisions against this control. |
| No decisions | This control exists in the catalog but no decision has ever been recorded against it. A dark control. |
Recording a decision against a control
A decision records the outcome of a PDP against a named control, scoped to a specific artifact. Use--fingerprint to identify the artifact the decision applies to — this is what allows kosli assert artifact --environment to later check that all required controls have passing decisions for that artifact specifically.
| Flag | Description |
|---|---|
--control | Required. The control identifier this decision is recorded against. |
--compliant | Required. Whether the control is satisfied: true or false. |
--fingerprint | The SHA256 fingerprint of the artifact this decision applies to. Scope decisions to an artifact so that assertions and environment policies can check compliance for that artifact specifically. Omit to record a trail-scoped decision instead. |
--artifact-type | The artifact type (e.g. docker, file). Provide this with the artifact name/path as the command argument instead of --fingerprint to have Kosli calculate the fingerprint. |
--name | The attestation slot name on the trail. |
--description | Optional human-readable context for the decision. |
--attachments | Optional evidence file(s) to attach (e.g. an evaluation report, a REGO policy output). |
--user-data | Optional path to a JSON file containing additional structured data to attach to the attestation. |
--compliant false decision makes the trail non-compliant. There are no restrictions on which flow or trail a decision can be recorded on — place it wherever makes sense in your process, typically at the point where the decision is actually being made (e.g. during a release preparation or promotion step).
A decision records the outcome of a PDP. How the PDP is implemented — running
kosli evaluate, executing a custom script, or using a third-party tool — is up to you. kosli attest decision records the outcome; it does not make the decision for you.Attaching evidence to a decision
Evidence attached to a decision explains why the decision was reached — not just that a control passed or failed, but what information was used to make that judgement. This is what auditors will ask for: the policy that was applied and the evaluation report that justified the outcome. A natural source of evidence is akosli evaluate report. kosli evaluate is a PDP: it runs a Rego policy against a trail’s evidence and writes the result to its output, but always exits 0 — it has no enforcement logic. The example below evaluates a trail, captures the full JSON report, reads the allow/deny result from that output, and records it as a decision. See Evaluate trails with OPA policies for a full walkthrough of kosli evaluate.
--attachmentscontaining the Rego policy (for reproducibility) and the full JSON evaluation report--user-datacontaining the violations, which appear in the Kosli UI as structured metadata on the attestation--compliantset directly from the evaluation result
Asserting artifact compliance
kosli assert artifact --environment is the Policy Enforcement Point (PEP). It checks that an artifact satisfies all requirements in the environment’s attached policy — including any controls listed under the controls key — and exits non-zero if it doesn’t. Use it as a pipeline gate before promoting an artifact to an environment.
| Flag | Description |
|---|---|
--fingerprint | The SHA256 fingerprint of the artifact to assert. |
--artifact-type | The artifact type (e.g. docker, file). Provide this with the artifact name/path as the command argument instead of --fingerprint to have Kosli calculate the fingerprint. |
--environment | Required. The Kosli environment whose attached policy the artifact is asserted against. |
End-to-end pipeline flow
The sequence below shows a single artifact moving through a build trail and a release trail, with the compliance decision made at release time and enforced by the release controller checking the environment policy.Referencing controls in environment policies
Environment policies define the requirements an artifact must satisfy before it can run in a given environment. You can require that specific named controls have a passing decision recorded — not just that the trail is generally compliant. This is the key distinction: rather than relying on trail compliance as a catch-all, you can make individual controls explicit policy gates.prod-policy.yaml
kosli assert in your pipeline. This abstracts the policy from the specific tooling your pipelines use: instead of “has an attestation of type snyk with zero criticals”, the policy expresses “control RCTL-1866 has been satisfied” — and the decision attestation carries the evidence of how that judgement was reached.
For the complete policy syntax, including attestation requirements and exceptions, see the Environment Policies page.
Viewing control compliance
Navigate to Controls in the Kosli app and select a control to see its detail view. Each control has three tabs: Decisions, Deployments, and Coverage.Decisions
The Decisions tab is the default view. It lists every decision attestation recorded against this control across all flows and trails, with the artifact, flow, trail, environment, who recorded the decision, when, and whether the outcome was compliant or non-compliant. Each decision also shows which version of the control definition was in effect when it was recorded. Use the flow, environment, and outcome filters to narrow the list.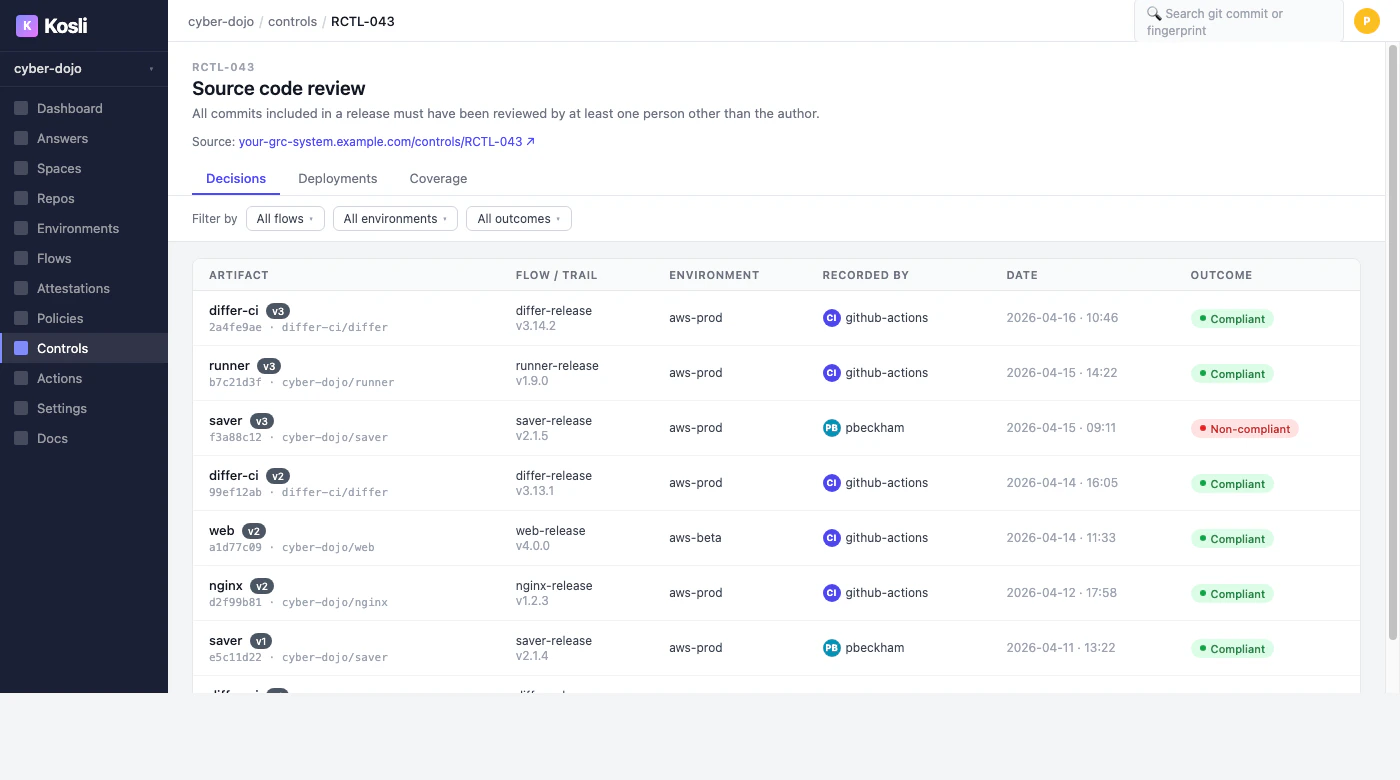
Deployments
The Deployments tab shows where artifacts with decisions against this control have been deployed, with compliant/non-compliant status per deployment, filterable by repository, flow, and environment.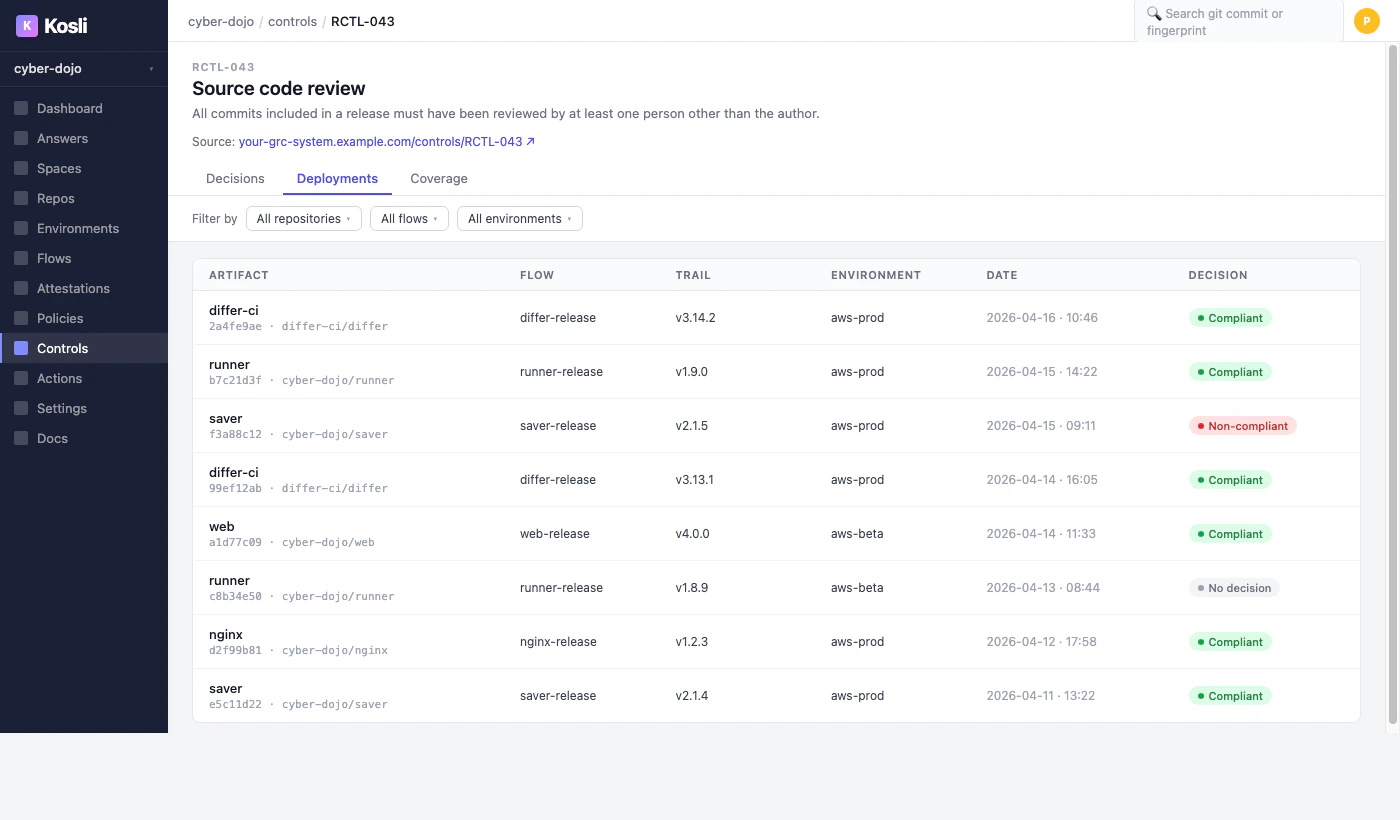
Coverage
The Coverage tab shows the ratio of deployments where a decision was recorded vs. those where it was not. This is the key metric: controls without decisions are the blind spots that auditors will ask about. Use the environment filter to compare decision recording rates across staging and production.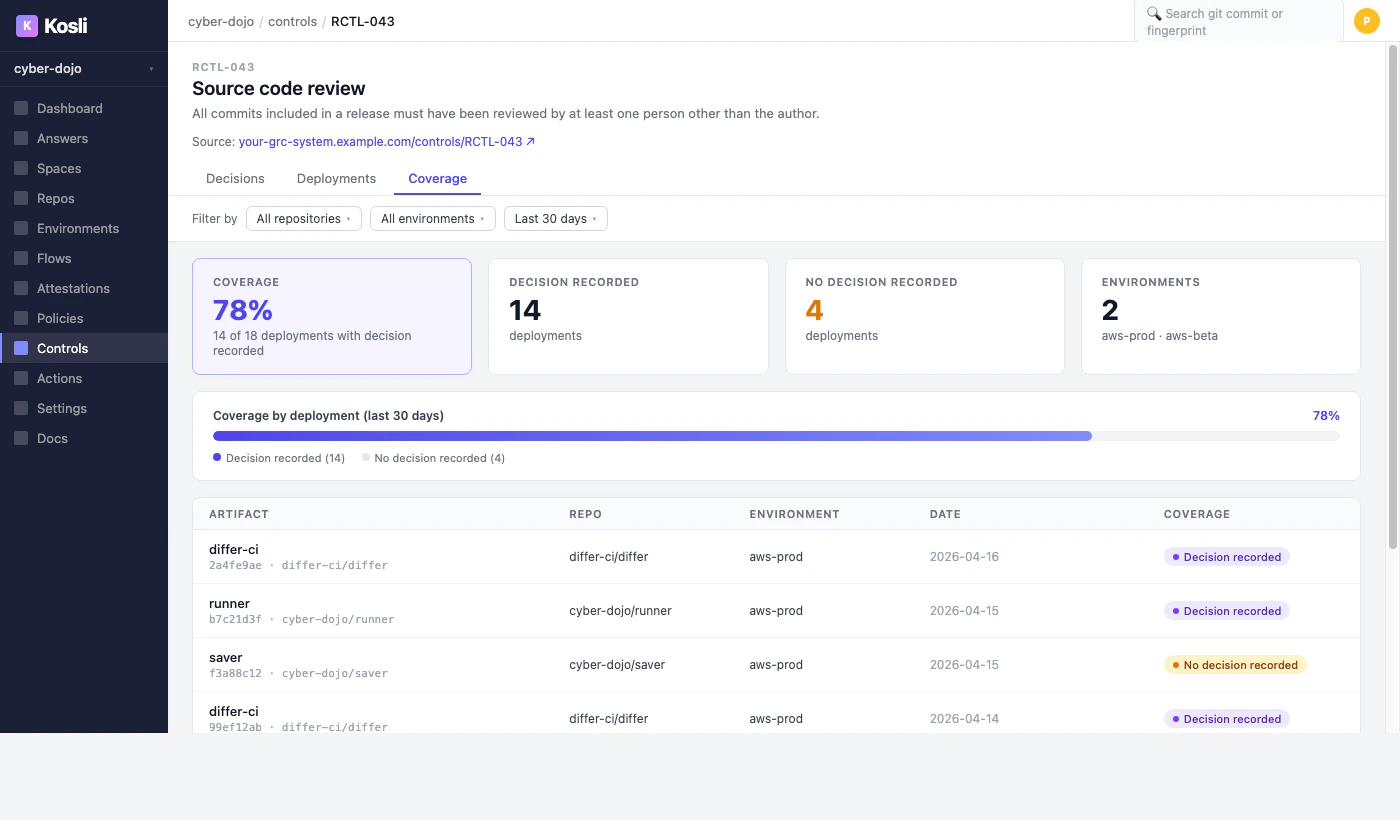
What you’ve accomplished
You have learned how to define controls in Kosli, record decisions against them from pipelines usingkosli attest decision as the PDP, enforce controls in environment policies, assert artifact compliance using kosli assert artifact --environment as the PEP, and view compliance across deployments.
Your controls catalog is now the bridge between the evidence Kosli collects and the requirements your auditors, control owners, and regulators care about. For each production change, you can now answer: “which of our controls have decisions recorded, and which don’t?”
From here you can:
- Learn more about environment policies
- Learn more about attestations
- Evaluate trails with Rego policies to automate decision-making
- Explore the Controls API reference for programmatic catalog management